I think its important to give an update on Dapper Secure Kernel Patchset, the technology underpinning the majority of security foundations found within Dapper Linux.
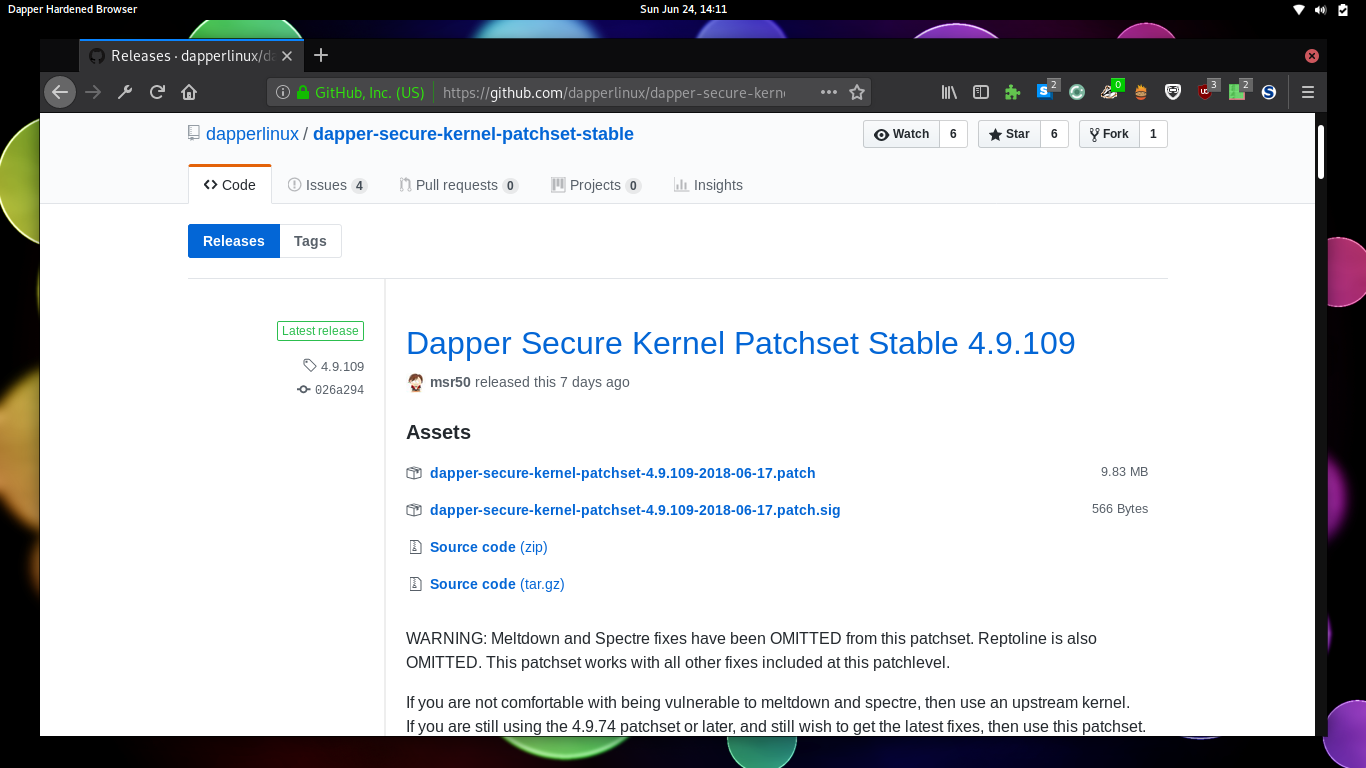
As we recall from the last blog post, Dapper Secure Kernel Patchset is a fork of the final grsecurity patchset from April 2017, which was version 4.9.24 at the time Open Source Security announced that public access to test patches will cease. I announced two forks, one, Dapper Secure Kernel Patchset, targets Linux 4.14 and is currently incomplete, and the other, Dapper Secure Kernel Patchset Stable, is now at 4.9.109 and is fully functional.
Its quite an achievement on getting Dapper Secure Kernel Patchset Stable from 4.9.24 all the way to 4.9.109. Thats 75 whole releases, and a cause for celebration! Some of those releases were straightforward, some not so. Some were routine code maintenance, and some were some in depth changes. Let's have a look at some of those.
Maintenance of Dapper Secure Kernel Patchset Stable was straightforward until 4.9.75. There were a few seperate forks around, mostly myself, Minipli and Alpine, who would fix merge conflicts and release a new patch once or twice a week. Then in January, everything changed with the announcement of Meltdown and Spectre, a class of vulnerabilities targeting hardware flaws in cpus which take advantage of speculation of branches of instructions. If you are here and reading this blog, you probably already know how they function.
But when it came to the patchset, I first knew something was up when I saw a large amount of merge conflicts when I sat down to maintain the patchset. It was far more than normal, about 12. These all made large modifications to the core and required a lot of work to get settled. I eventually got everything merged, and quickly found after compiling that I was going to have a hard time getting it to boot.
It turns out, that KAISER, the PTI code which was pushed to the 4.9 branch by upstream, was incompatible with PaX, and will likely never be. The grsecurity twitter explained that upstream grsec patches will have PTI disabled, and functionality placed in UDEREF. Now, modifications to UDEREF to mitigate meltdown are a little out of my depth, even with the level of understanding of the patchset I hold. I waited, to see what Minipli would do in his fork, since discussion was ramping up on his github issue tracker.
Problem is, Minipli never did make any more releases. Six months after the fact, his tree still shows his latest release to be 4.9.74, the version before Meltdown.
Around mid May, I started to get a little worried about using a kernel missing 4 months of security patches, I decided to try and start performing maintenance again. I got the raw diffs from 4.9.74 -> 4.9.75 and went through each patch hunk, and pulled out everything not related to Meltdown or Spectre, and set up scripts to reverse those incompatible patches.
In that first release, it turned out the only compatible patch hunk was the modification to the Makefile to denote the kernel was now at version 4.9.75. I kept on going, and started 4.9.76, which contained the groundwork for Retpoline.
I started a new process of always getting patch hunks from one version to the next, like 4.9.75 -> 4.9.76, and made an "omitted-patches" folder in my source tree. This folder holds files of "omitted" patch hunks which are reversed, and "included" patch hunks which are allowed to remain in the tree.
I always make sure that "omitted" + "included" = "raw diff". From here, I would push forward Kernel versions, and made my way to 4.9.80, shuffling patches between omitted and included as necessary. From there, I went and commented on one of Minipli's github issues, and started getting replies from interested users.
Maintaining this patchset is starting to get tough, but I won't give up! Dapper Secure Kernel Patchset offers a level of security which is hard to find elsewhere, and I don't want the world to lose such incredible advancements. I will continue to do my best to offer this patchset for Linux 4.9.x - Matthew Ruffell, Founder.
From there, I spent two weekends straight forward porting Dapper Secure Kernel Patchset Stable from 4.9.80 all the way to 4.9.106, using the omit scripts to reverse any patches related to Meltdown or Spectre. Over the past few weeks, I am back to the normal routine of making releases in tune with upstream, and currently sit at 4.9.109.
Things left to do:
- Complete GCC 8 port.
- Slowly merge in base Retpoline support.
- Complete Retpoline support.
- Decide what to do with Meltdown.
For the future, I need to work on finishing GCC 8 support, something I have spent much time on recently, but am currently stuck on, and beginning to start merging Retpoline and enabling its functionality.
Upstream support for Linux 4.9 will end in December. That is not very far away now, and I should be able to keep Dapper Secure Kernel Patchset Stable maintained until then. After that, I am not sure what will happen. It would probably be unwise to use 4.9 any longer than that, since it would be two years old, and likely Linux 5.0 would be out. The plan is to potentially start contributing to upstream, which will help we transition into a real kernel developer, instead of someone who maintains a fork.